Salesforce Org-to-Org SSO Integration
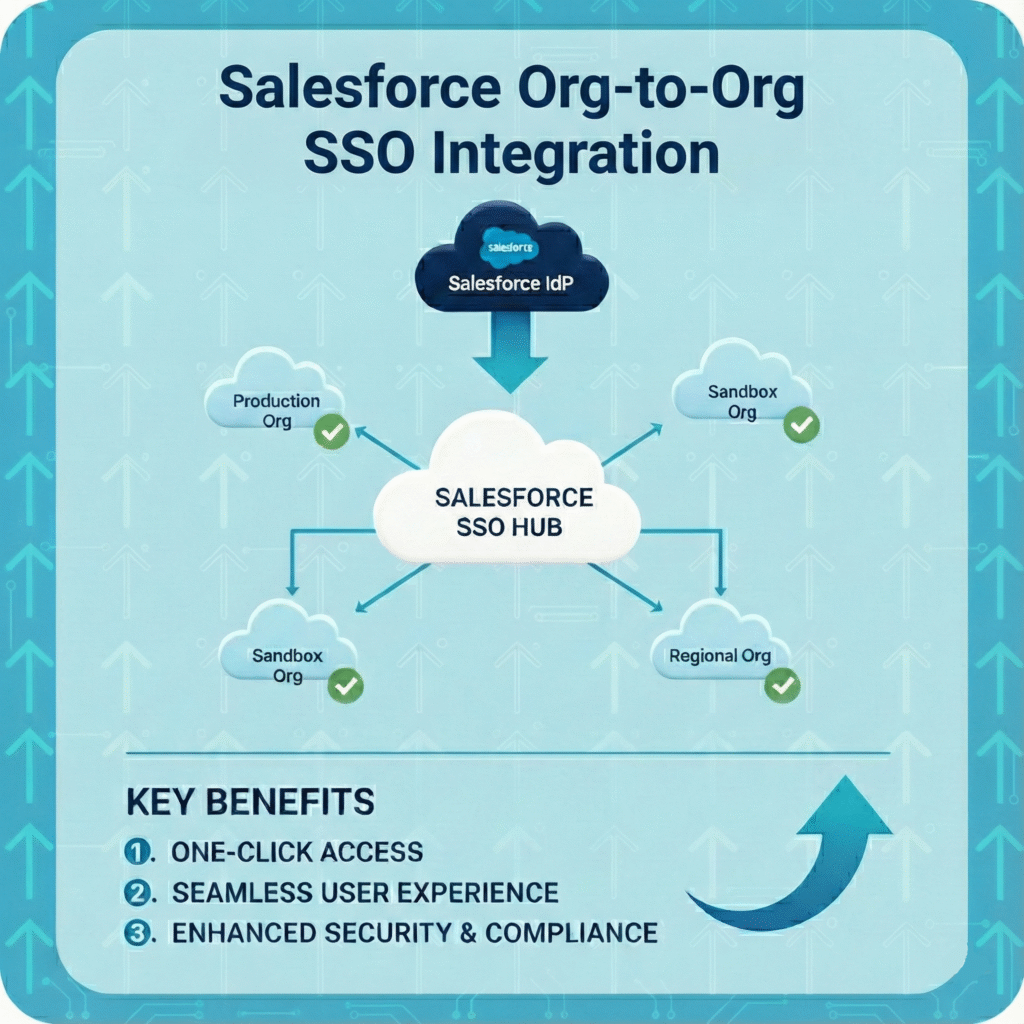
For organizations managing multiple Salesforce instances—perhaps due to mergers, global operations, or strategic division of business units—the challenge of user access and credential management is significant.
Salesforce-to-Salesforce Org-to-Org Single Sign-On (SSO) is the essential solution, allowing users to move from their primary Salesforce instance to a secondary one without needing to re-enter credentials, ensuring a unified and secure experience across the enterprise.
Challenge
Without a dedicated Org-to-Org SSO setup, managing access between two Salesforce environments is cumbersome and risky.
The Salesforce-Specific Problem:
-
-
- User Sync & Duplication: Users must be created and maintained in both the primary (Identity Provider) and secondary (Service Provider) Salesforce Orgs.
- License Overhead: Managing duplicate user records can complicate licensing and administrative audits.
- Credential Fatigue: Users must manage two separate sets of Salesforce credentials, leading to password sharing, reuse, or forgotten passwords.
- Manual Access Control: Revoking a user’s access in one Org does not automatically revoke it in the other, creating a potential security loophole.
-
Solution
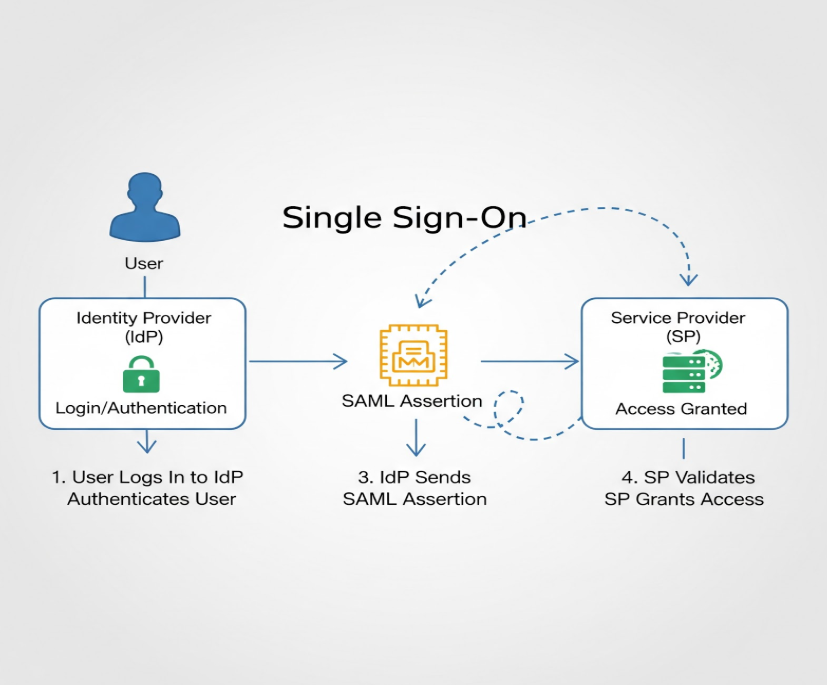
Salesforce’s built-in Identity and Connected App features make SAML-based Org-to-Org SSO a robust solution. The goal is to establish a secure trust relationship between the two Orgs.
Identity Provider Org:
-
- The Identity Provider Org is the primary Salesforce instance that authenticates the user and asserts their identity to the Service Provider Org.
- This is the organization where the user signs in once.
Service Provider (SP) Org
-
- The Service Provider Org is the secondary Salesforce instance that trusts the Identity Provider’s assertion and grants the user access without a second login.
- This is the organization that the user is trying to access seamlessly.
Implementation Steps
1- Configure the Identity Provider (IdP) Org:
-
-
- Create Certificate: Log in to the Org you want to use as the Identity Provider. Go to Setup > Certificate and Key Management > Create self Signed certificate.
- Create Certificate: Log in to the Org you want to use as the Identity Provider. Go to Setup > Certificate and Key Management > Create self Signed certificate.
-
-
-
- Enable IdP: Log in to the Org you want to use as the Identity Provider. Go to Setup > Identity Provider > Enable Identity Provider and select the certificate.
- Enable IdP: Log in to the Org you want to use as the Identity Provider. Go to Setup > Identity Provider > Enable Identity Provider and select the certificate.
-
-
-
- Get Metadata: Copy the Issuer Id and download the Metadata XML file.
- Get Metadata: Copy the Issuer Id and download the Metadata XML file.
-
2- Configure the Service Provider (SP) Org:
-
-
- Setup SSO: Log in to the Service Provider Org and set up Single Sign-On.
- Create SAML SSO: Create a new SAML SSO setting by uploading the Metadata file downloaded from the IdP Org. This will automatically fill in most details, including certificates.
-
-
-
- Finalize Settings: You can change the name of your choice. Keep the SAML Identity Type as Federation ID and Request Binding as POST.
- Finalize Settings: You can change the name of your choice. Keep the SAML Identity Type as Federation ID and Request Binding as POST.
-
-
-
- Get Endpoints: Save the configuration. You will now have the login and logout Endpoint URLs from the Service Provider.
Note: Make sure your SAML is Enabled:
- Get Endpoints: Save the configuration. You will now have the login and logout Endpoint URLs from the Service Provider.
-
3- Create the External client App on the IdP Org:
-
-
- Connected App: In the Identity Provider Org, create a External Client App.
- Configure SAML: Provide the details from the Service Provider:
- Entity Id: Same as SSO Entity on the Service Provider (domain of the Identity Provider).
- ACS URL: The Login URL from the Service Provider.
- Single Logout URL: The Logout URL from the Service Provider.
- Issuer: Same as the Service Provider’s Issuer.
- Certificate: Use the Request signing certificate.
- Save: Save the record.
-
Note: Make sure you have provided the access to the user and the Federation ID of user is same in both the orgs
Testing
1- Using SAML URL
-
- Go to the App manager and open your External Client app.
- Under SAML Login Information, you will find the IDP login link. Clicking this link should navigate you to the Service Provider Org.
2- Using App Launcher
-
- Alternatively, you can search for your connected app in the App Launcher.
- If you want to open a particular page, you can provide the Page URL in the Connected App’s Start URL.
Results
Once the SAML handshake is complete, users can seamlessly transition between Salesforce Orgs, leading to immediate improvements:
-
-
- Zero-Credential Access: Users sign in once to the IdP Org and are granted instant access to the SP Org, eliminating the need to log in twice.
- Centralized Identity Control: The primary Org maintains complete control over the user’s identity and access status, simplifying security management.
- Simplified Auditing: All user activity is tied to their primary identity, making compliance and security audits across the two Orgs much cleaner.
- Federation ID Focus: Utilizing the Federation ID as the unique identifier ensures that user records across the two Orgs are correctly linked during the SSO process.
-
